The problem lies in the PC device driver side. When this device exposes a mouse top-level collection, built-in HID device driver and OS handle the rest - it works like mouse for any application on the PC. When it exposes a digitizer top-level collection, however, there is no built-in device driver for HID side on Windows. You also need to select HID Input layer support (below) if you want to use keyboards, mice, joysticks and the like. As well as Uninterruptible Power Supply (UPS) and monitor control devices. You can't use this driver and the HIDBP (Boot Protocol) keyboard and mouse drivers at the same time.
- Multi-monitor Usb Mouse Hid Input Devices Driver Updater
- Multi-monitor Usb Mouse Hid Input Devices Driver Windows 7
- Multi-monitor Usb Mouse Hid Input Devices Driver Download
- Multi-monitor Usb Mouse Hid Input Devices Driver
Contents:
HID-Compliant Mouse Not Working Overview
HID devices out of work is very common on different computers, for instance, HID-compliant mouse does not work on Windows 10. For some people, other HID-compliant devices problem can also come to you as well when you connect HID device, such as Dell HID-compliant mouse, to the PC.
Just like mouse cursor missing on the desktop, HID-compliant mouse missing can also be rather annoying, which means the mouse cannot work properly on your PC.
Some users have no idea about the Logitech HID-compliant mouse on Windows 10, let alone know how to fix hid-compliant mouse not working error.
What is HID-Compliant Mouse?
HID refers to Human Interface Device. And the HID-compliant devices often belong to the human input and output, such as the USB mouse, USB Pen and USB keyboard. So all the USB mouse will be a HID-Compliant device such as Logitech MX Master. Therefore, the USB mouse not working can also belong to a kind of HID devices problems. At the time you connect your Logitech HID-compliant mouse to PC, Windows 10 would prompt you that a hid device is recognized.
Why would Logitech HID-Compliant mouse stop working?
The reasons for HID device of Dell or any other mouse failed to work can be mainly divided into two parts.
The first one is the HID-compliant mouse driver Windows 10.

Sometimes,the HID device is missing in device manager. That is why the USB mouse or Logitech wireless mouse would not be recognized, thus not working on Windows 10. Under this circumstance, you need to update Logitech Hid-compliant mouse driver and install it on your PC.
The other one is the HID devices condition.
No matter you are using HID-compliant mouse or touch screen, Logitech or Dell, when the HID device physical condition goes wrong, you will meet Windows 10 Logitech mouse not working, which can be called a type of Human Interface device problem if yours is Logitech hid-compliant mouse.

Hence, to get HID mouse back to laptop or desktop, you are supposed to check HID-compliant mouse hardware condition and download HID-compliant mouse driver for Windows 10 to see if to install an HID-compliant device driver can help.
5 Ways to Fix HID-Compliant Mouse Not Working Windows 10
To help you solve Logitech or Dell HID-compliant mouse work failed error on Windows 10, you are suggested to refer to the following five ways, which can also be applied to other HID devices problem.
Solutions:
Solution 1: Check HID-Compliant Mouse Hardware
To make sure your Human Interface Device Compliant mouse is in perfect condition and get the computer to recognize the HID-compliant mouse, you should check the following things to make sure you have the compatible HID device with Windows 10.
1. Check Mouse port by plug another intact mouse into this HID-Compliant mouse port.
2. Check the HID-Compliant mouse by using it on another PC.
If you have examined the HID device port, it can make other USB mouse work well and also the HID-compliant mouse can work well on another computer, which denotes that you are using the compatible HID mouse on Windows 10.
But if the HID-compliant mouse not working on Windows 10 remains on your computer, maybe it is the HID-compliant mouse driver issues that cause Windows 10 HID devices not working, on that occasion, you would better go on to fix Windows 10 HID-compliant driver.
Related: Fix USB Port Not Working on Windows 10
Solution 2: Uninstall HID-Compliant Mouse Driver
Just as discussed before, if your Logitech HID-compliant mouse driver is missing or corrupted on Windows 10, the HID-compliant mouse cannot work, too. In this way, you should uninstall the HID mouse driver in device manager and then download and install the HID-compliant mouse latest driver.
1. Open Device Manager.
2. Expand Mouse and other pointing devices.
3. Right click HID-Compliant mouse to Uninstall it.
4. Confirm Uninstall device. Here you need to click Uninstall to confirm the uninstalling.
5: Under Action, click Scan for hardware changes or you can just restart your PC to let Windows 10 automatically reinstall a new HID-Compliant mouse driver for you.
In many cases, though Windows 10 can find the Logitech HID-compliant mouse driver for you, you will also find that it cannot get your HID-compliant mouse back to work correctly, for Windows 10 failed to get the latest one for your HID-compliant mouse. You still cannot connect HID devices to a computer, such as HID-compliant mouse and HID-compliant keyboard.
Solution 3: Install HID-Compliant Mouse Driver on Windows 10
If you failed to download the compatible or latest Logitech HID-compliant mouse driver using the device manager, you can take advantage of Driver Booster to help you fix this problem.
Driver Booster is a professional and absolutely safe driver tool. With the help of it, it can automatically download the latest and advanced HID-compliant mouse driver and then you can install Windows 10 HID mouse driver with the instructions.
Download, install and run Driver Booster on your computer.
1. Click Scan. That is to let Driver Booster scan your computer for any missing, corrupted or even damaged driver. Here if your HID-Compliant mouse is not working well on Windows 10, maybe you can see the HID-Compliant mouse driver showing up in Driver Booster scanning results.
2. Select Human Interface Device, and click Update.
You will find that Driver Booster helps you update latest HID-compliant mouse driver, which makes your HID-compliant mouse out of work or unrecognized issue disappeared from Windows 10. As you have solved HID device has a driver problem for your PC, such as Dell, ASUS.
At that moment, you can finally fix your Windows 10 mouse issues if you have downloaded Windows 10 HID mouse driver for PC. While as for the HID-Compliant touchpad missing error, it is also feasible to use Driver Booster to help fix the HID device driver issue.
Solution 4: Restart HID-Compliant Mouse Services
Sometimes, if you have performed a device or program for a long time, it will go wrong without premonition. Similarly, once you have used HID-compliant device too much, The HID-complaint mouse keeps not working on Windows 10 or just stops working unwittingly. So you may as well try to restart the related services of HID-compliant mouse.
1. Input Services in the search box and click Enter to get into Services window.
3. In Services window, locate Human Interface Devices Service and right click it to Restart it.
Then you can see that Windows 10 HID-compliant mouse get recognized or unable to properly used error and is working well as you control it.
Solution 5: Uninstall KB4074588 Update
According to the reports from many users, after KB4074588 Windows 10 Update, HID-compliant mouse stopped working, in some cases, other HID devices, such as HID-Compliant keyboard, or HID-compliant touchpad can also be out of work.
In this way, it is wise and feasible to remove the KB4074588 updates so as to fix hid compliant mouse on Windows 10.
1. Go to Start > Settings > Update & security.
2. Under Windows Update, click Update history.
3. Choose to Uninstall Updates.
4. All the Windows 10 updates will be available in the following window. Select the update KB4074588 and decide to Uninstall it.
5. Restart Now. You should restart your PC to apply these changes.
When you log on to Windows 10 again, you can try to connect Logitech HID-compliant mouse to the computer and it is natural that the HID-compliant mouse failed to work issue after Windows 10 update KB4074588 has been resolved.
Related: 4 Things You Should Know about Windows 10 Updates
However, once you find Windows 10 Hid devices problem persists, manage to enter safe mode to detect the mouse issues in a minimal set of programs.
To conclude, this tutorial aims for teaching you how to fix the HID-Compliant mouse not working issue on Windows 10. You can try to uninstall and reinstall the Windows 10 HID-Compliant mouse driver manually or automatically by Driver Booster, the automatic driver downloading or updating tool. Or you can also choose to restart the related services.
More Articles:
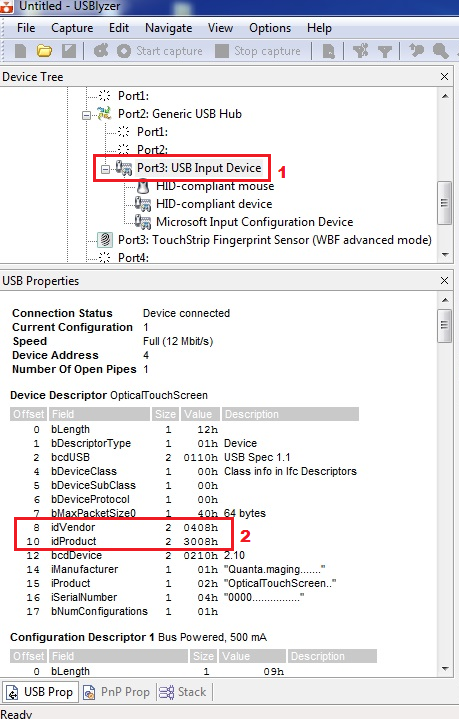
The Universal Serial Bus (USB) standard has been with us for many years, but making USB devices is still a daunting task. The USB specification comprises thousands of pages spread over dozens of documents, and although good books have been written on the subject, they are rarely shorter. In addition, the application programming interface (API) offered for programming USB devices is often complex and intricate. This article describes how to program your own software-based USB devices. It is not limited to standard class devices, but also presents a way to implement any device, whether it complies with a standard class or not.
Table of Contents
The USB Way Of Thinking
To understand USB, one has to understand a dozen terms that form the foundation of the USB world. USB separates the host from the device: there is one host, connected to multiple devices. The host initiates all traffic and schedules it on the USB bus.
A device is a physical box at the end of the USB cable that identifies itself to the host by passing it a device descriptor and a configuration descriptor. These descriptors are binary data that describe the capabilities of the USB device. In particular, the configuration descriptor describes one or more interfaces, where each interface is a specific function of the device. A device may have multiple interfaces. For example, a USB device that comprises a keyboard with a built-in speaker will offer an interface for playing audio and an interface for key presses.
Each interface comprises a series of endpoints that are the communication channels between the host and the device. Endpoints are numbered between 0 and 15 and may be IN endpoints or OUT endpoints. These terms are relative to the host: OUT endpoints transport data to the device, and IN endpoints transport data to the host (Fig. 1). The are four types of endpoints:
- Bulk endpoints reliably transport data whenever it is required. Bulk data is acknowledged and therefore fault-tolerant.
- Isochronous endpoints are for transporting real-time data. A fixed bandwidth is allocated to them. The host allocates this bandwidth and will not allow an isochronous endpoint to be created if no bandwidth is available. In contrast, bulk endpoints have no guaranteed bandwidth.
- Interrupt endpoints are polled occasionally by the host and enable a device to report status changes.
- The control endpoint (endpoint 0) is used to perform general operations, such as obtaining descriptors, or performing a control-operation such as “change the volume” or “set the baud rate” on any of the interfaces.
1. Traffic over the USB bus is bidirectional.
USB traffic is organized in frames. Frames are marked by the host sending a start of frame (SOF) every 125 µs (for high-speed USB) or every 1 ms (for Full Speed USB). Isochronous endpoints are allocated a transfer in every frame. Interrupt endpoints are polled once every so many frames, and bulk transfers may happen anytime when the bus is not in use.
As an example, the aforementioned keyboard with built-in speaker has at least two endpoints: an isochronous OUT endpoint to transfer audio data to the speaker, and an interrupt IN endpoint to poll the keyboard. Suppose the speaker is a mono-speaker with a 48-kHz sample rate. The host then will send six samples of data every 125 µs (six samples/0.000125 seconds = 48,000 samples/second). If a sample occupies 16 bits, the host will reserve enough bandwidth to send a 96-bit OUT packet in every 125-µs frame. This consumes around 0.5% of the USB bandwidth. The remaining 99.5% is free for other interfaces or other USB devices on the same bus.
Specifying And Discovering Device Capabilities
The host initiates all USB traffic. When a device is plugged in, the host first requests the device-descriptor. This descriptor comprises two sets of information that inform the host of the basic capabilities of the device: the device class and the vendor ID/product ID (VID/PID).
The class and subclass can be used to specify a device with generic capabilities. A USB speaker advertises itself as class Audio-2.0. A keyboard advertises itself as a HID-class (human interface device) device. The previous example of a device with both a speaker and a keyboard advertises itself as a Composite device class.
USB devices that comply with a specific USB class enable cross-vendor and cross-platform compatible USB devices. The USB specification specifies hundreds of device classes that enable the generic implementation of, for example, Ethernet dongles, mixing desks, or flash disks and enable operating systems to provide generic drivers for these classes.
There are cases where the USB device does not fit a specific class or where the class specification is too constrained for a particular device. In that case, the class of the device must be described as vendor-specific. The operating system (OS) shall then use the VID and PID to find a vendor-specific driver.
When the device descriptor has been dealt with, the OS assigns the USB device a number, informs the USB device of the number (it is being enumerated), and requests the configuration descriptor that specifies each interface in detail. In the earlier example, the configuration descriptor will specify two interfaces: one interface of class USB-Audio-2.0 with a single channel output endpoint running at 48 kHz only, the other interface of class HID that specifies a single keyboard with a specific keymap.
There are cases where the USB device does not have any OS support and it should interact with a user program directly. In that case, a generic driver such as the open-source libusb driver that allows an application program to communicate with any USB device can be used. Typically, the device will be advertised as vendor-specific. Through the libusb interface the user program can detect a device with a VID and PID that it wants to interact with, claim an interface, open an endpoint, and send IN and OUT requests to that endpoint.
What To Do With Your Data
The enumeration of the device typically requires static descriptors to be sent to the host. The difficult bit is creating the descriptors. Serving them is simple, as that is the only task required of the device at the time. After enumeration, data may arrive or be requested on all endpoints in quick succession. This requires an interface between the software that deals with the function of the USB device (e.g., playing audio or monitoring keystrokes on the keyboard) and the low-level USB protocol. Prior to designing this interface, let’s look at how to handle data on various types of endpoints.
Bulk endpoints are the easiest to deal with. Since each data transfer is acknowledged, it is possible to send a negative acknowledge (NAK) stating that the device is not yet ready to deal with the endpoint. For example, if software is dealing with some other part of the device, or if data is simply not yet available (for example, a read from flash memory is not yet completed), the low-level USB driver can send a NAK.
However, sending NAKs has a downside. The only sensible option for the host is to retry the request, potentially creating a long series of requests that are aborted by NAKs. This wastes USB bandwidth that could have been used by other endpoints or devices. In addition, the host software is blocked until the device answers. Hence, NAKs should be a last resort. It may be more appropriate to send partial data than to NAK an IN request. In the case of an OUT request, little can be done. If there is no room to accept the data, then a NAK is the only answer. However, it may be more appropriate to introduce a high-level protocol that will not allow an OUT request until there is space.
Isochronous endpoints are more difficult to deal with because they are not acknowledged. The transmitter (in either direction) assumes that the data arrives. Since there is no acknowledgement on an isochronous endpoint, there is no possibility to send a NAK. Hence, if the device is not ready, the only course of action is to drop the data from an OUT packet or to send no data for an IN packet.
Although this may seem harsh at first, remember that the purpose of an isochronous endpoint is to transmit real-time data in a guaranteed time slice of the USB bus. If the device does not have room to store the OUT data, data is probably not dealt with in real-time. Dropping is a sensible course of action. If no data is available to answer an IN request, then the device has not collected enough data. A sensible course of action is to transmit whatever data is present, or possibly no data at all.
Assuming that the data can be processed or produced in real time, it is easy to compute the buffer requirements for an isochronous endpoint:
- For an OUT endpoint, the worst possible case is that the host posts one OUT request right at the end of a USB frame, and then immediately after the start of frame (SOF) it posts a second OUT request. This means that two OUT requests, carrying 250 µs of data, are received in quick succession. Hence, the buffering scheme must be able to buffer at least 250 µs worth of data. As long as the program does not consume data from this buffer until the SOF following the first packet, the buffer will never empty, providing a continuous data stream from host to device.
- For an IN endpoint, the worst case is similar. The host could perform two IN transfers in short succession just before and immediately after a SOF. This means the IN buffer needs to be at least 250 µs too, and the buffer should contain125 µs at the start of each frame.
It is worth comparing bulk and isochronous transfers from a perspective of coping with errors. In bulk transfers, the data itself is critical. The host and device can retry and slow down, as long as the data is transferred correctly, and this transfer must be acknowledged. For an isochronous transfer, the timing is critical. Either side can throw data away, as long as the real-time characteristics of data further along in the stream are adhered to. (Of course, the decision to drop data should not be taken lightly as it will have an impact on the fidelity of, for example, a video or audio stream.)
The>
2. The USB software architecture is designed for handling multiple endpoints.
Note that one thread per endpoint may not be required and may not be the most elegant method. Given that only one transaction happens at a time (the third point), we can create a version of the system that relies on fewer threads in the system. Suppose that we want to implement a synchronous protocol over two endpoints where the host will always transmit data over a bulk OUT endpoint, prior to receiving data on an associated IN endpoint. This protocol requires only a single thread that handles OUT and IN transactions in order on that endpoint.
This optimization is not without risk. Using a single thread per endpoint naturally caters to the situation where the host program was aborted and restarted between the OUT and IN transaction. In this case, the sequence of transactions seen on the device will be ..., OUT, IN, OUT, IN, OUT, OUT, IN, ..., and the thread dealing with OUT transactions must swallow the extra OUT. When optimized away to a program that sequentially consumes OUT and IN in order, this program must be written so that at any time it may expect the protocol to reset.
The third point enables a further optimization. A single thread can deal with all bulk traffic on all interfaces, optimizing multiple endpoints into a single thread (Fig. 3). The single thread receives a request (IN or OUT) on any endpoint, dealing with that request, whereupon it moves on to the next request, possibly on a different endpoint. If the next request arrives before the last request has been dealt with completely, the USB device library sends NAKs, temporarily holding up the host. This optimization has one disadvantage, which is that the single thread must keep state for each endpoint and is effectively context switching on each request. We will show an example of this later.
3. Multiple endpoints can be optimized into a single thread.
The same optimization cannot be applied to isochronous endpoints. If we had a single thread dealing with all isochronous data, it would involve FIFOs for each endpoint from which the thread will read data or post data. These FIFOs will increase latency, which is often undesirable.
Multi-monitor Usb Mouse Hid Input Devices Driver Updater
The rest of this article discusses two examples of the software architecture and optimizations. One example uses vendor-specific drivers and mostly bulk endpoints (JTAG over USB), and the other shows a standard USB class with mostly isochronous endpoints (Audio over USB).
JTAG Over USB
For debugging programs on embedded processors, it is common to use a protocol such as JTAG for accessing the internal state of the processor and to use a program such as gdb to run on a PC to interpret and modify state, set breakpoints, single step, and so on. USB can be used to provide a cross-platform portable transport layer between the PC and JTAG wires.
These devices are often called JTAG keys. In addition to JTAG, they often contain a UART for text I/O from the embedded program. JTAG keys do not follow any standard USB class. Hence, the descriptor labels them as vendor-specific, and it is up to us to define an endpoint structure that is fit for purpose. One endpoint structure would use six endpoints:
- Two endpoints that control the USB device itself (endpoint 0 IN and OUT, required by USB)
- An IN and OUT endpoint for JTAG traffic
- An IN and OUT endpoint for UART traffic
Since there is no USB standard, we can define the protocol for the JTAG traffic and choose a set of commands such as “send a clock with TMS high” or “read the program counter.” On the host side, our program can use libusb (an open-source USB driver library) to search for a device with our VID and PID, claim the interface, and then use the libusb interface to send IN and OUT transactions to both the JTAG and UART endpoints.
Figure 4 shows a suitable software architecture for the device-end. Given that all endpoints are for bulk traffic, they can all be mapped onto a single thread and have two separate threads to deal with the state machines for JTAG traffic and UART traffic. Figure 5 shows a sample implementation.
4. JTAG over USB employs multiple endpoints.
5. A JTAG interface can be implemented using USB hardware and a standard 20-pin JTAG connector.
Audio Over USB
As an example of a standard USB device, let’s discuss Audio over USB. The Audio-2.0 Class standard allows interoperability of devices on platforms: a consumer can buy a USB microphone or USB speakers and plug it into any computer that supports Audio over USB. The number of channels, sampling rate, and sample depth can be varied to support anything from low-channel-count consumer devices to high-quality, high-channel-count professional audio.
Devices that are more complex also are supported. The descriptor has a syntax for describing mixers, volume controls, equalizers, clocks, resampling, MIDI, and many other functions, although not all of those functions are recognized by all operating systems.
On the host side, all USB traffic carrying audio samples is directed to the USB-Audio driver, which interacts through some general kernel sound interface with the program using audio, such as Skype. Other data, such as MIDI, can be handled through a separate interface by a separate driver.
The device is designed to use USB Audio Class 2.0, and the standard specifies the endpoints that we need to use. If the application has to support MIDI, stereo in, and stereo out with a clock controlled by the device, then the standard dictates that there shall be seven endpoints:
- Two endpoints that control the USB device itself (endpoint 0 IN and OUT, required by USB)
- An isochronous IN endpoint for the I2S analog-to-digital converter (ADC)
- An isochronous OUT endpoint for the I2S digital-to-analog converter (DAC)
- An isochronous IN endpoint for feedback on the clock speed
- A bulk IN endpoint and bulk OUT endpoint for MIDI
The endpoints for the ADC and DAC have one IN and OUT transaction every microframe, every 125 µs. Assuming that the DAC and ADC operate with a 96-kHz sample rate, 12 samples are sent in each direction every 125 µs. Note that there are two independent oscillators: the device controls the 96-kHz sample rate, and the host controls the 125-µs microframe rate.
Multi-monitor Usb Mouse Hid Input Devices Driver Windows 7
As these clocks are independent, they will drift relative to each other, and there won’t always be 12 samples in each transfer. The vast majority of the transfers will have 12 samples, but sometimes there will be 13 or 11 samples.
Multi-monitor Usb Mouse Hid Input Devices Driver Download
The device uses the third isochronous endpoint to inform the host of the current speed. It is sampled once every few milliseconds and reports the current sample rate in terms of samples per microframe. The MIDI endpoints carry MIDI data as and when available. The standard provides flexibility, allowing us to easily add more audio channels or audio processing.
Figure 6 shows the software architecture for this device. Unlike the previous example, there is little that can be optimized. The class specification dictates the endpoint structure. With three isochronous endpoints, it is advisable to have three processes ready to accept and provide data on these endpoints. The only optimization that is feasible is for a single thread to handle Endpoint 0 and the MIDI endpoints (Fig. 7).
Multi-monitor Usb Mouse Hid Input Devices Driver
6. Audio over USB software employs multiple endpoints.
7. Audio over USB hardware can be implemented with XMOS hardware.
Summary
USB devices comprise many interfaces that run concurrently and endpoints that are either bulk or isochronous. Bulk endpoints are for reliable data transport between host and device, whereas isochronous endpoints are for real-time data transport.

When programming USB device endpoints, it is easiest to see those endpoints as individual software threads. Some of those can be mapped onto a single thread, but the programmer has to understand the consequences. In particular, mapping multiple isochronous endpoints onto a single software thread will introduce an (unpredictable) latency in the real-time stream.
References
- Audio class specification: http://www.usb.org/developers/devclass_docs/Audio2.0_final.zip
- Libusb documentation: http://libusb.sourceforge.net/api-1.0/
